How Many Static Proxies Do You Need? A Planning Worksheet for Warm-Up, QA, and Repeat Logins
How Many Static Proxies Do You Need? A Planning Worksheet for Warm-Up, QA, and Repeat Logins
If you are buying static proxies for account warm-up, repeat logins, or recurring QA, the safest default is not one proxy per total account. A better starting point is one proxy per concurrently active identity group, plus a small spare pool for replacement and isolation.
That means a team running 20 accounts does not automatically need 20 static proxies. If only 6 to 8 identities are active at once, and the work is split carefully, the first batch may be closer to 8 to 12 proxies. If the workflow is trust-sensitive and accounts must look stable over time, the number moves up. If the job is mostly internal QA or low-friction monitoring, the number can stay lower.
If you have not yet chosen between residential-looking stability and cheaper infrastructure stability, start with Static Residential vs Static Datacenter Proxies. This article assumes you already know you need a static endpoint and now need to size the batch.
The short answer: buy for concurrent identities, not total accounts
Static proxy planning is a capacity question, not a collection hobby. The goal is to give each identity enough continuity that it does not constantly change network shape, while still keeping cost under control.
The fastest rule of thumb is:
- Count how many identities need to be active during the same time window.
- Separate trust-sensitive work from low-friction QA or monitoring.
- Add 15 to 30 percent spare capacity for replacement, cooldowns, and testing.
- Increase isolation if a failed account is expensive to recover.
If you only remember one line, remember this: concurrency drives proxy count more than raw account count does.
Static proxy sizing table
| Workflow shape | Identity sensitivity | Starting proxy ratio | Why this is usually enough | When to increase the count |
|---|---|---|---|---|
| Account warm-up with repeat logins | High | 1 proxy for each active account, plus 20 to 30% spare | Warm-up depends on stable returning identity | Increase if accounts are valuable, geo-sensitive, or frequently reviewed |
| Repeat-login operations with staggered schedules | Medium to high | 1 proxy for every 1 to 2 active accounts, plus spare | Not every account is active at once, but continuity still matters | Increase if accounts share risky timing or repeated challenge history |
| Internal QA, uptime checks, storefront testing | Low to medium | 1 proxy for every 2 to 4 active sessions | The work values stability more than residential realism | Increase if test environments geo-lock or rate-limit aggressively |
| Support recovery and account remediation | High | 1 dedicated proxy per recovery case | Recovery flows punish sudden network changes | Increase if support teams need country consistency or long case windows |
| Mixed workloads in one team | Mixed | Split by lane before sizing | One blended number usually hides the real need | Increase if warm-up and QA are sharing the same pool |
For teams that just need a stable endpoint class, the main product category is Static Proxies. If you already know the workload is identity-sensitive, compare the budget impact against Static Residential Proxies Pricing. If the job is mostly lower-friction QA or predictable service traffic, benchmark the cheaper lane against Static Datacenter Proxies Pricing.
How to estimate your starting batch
1. Count active identities, not named accounts
Ask how many identities are live in the same hour, not how many exist in the spreadsheet. A parked account does not need a dedicated proxy during that window.
2. Split the work into lanes
Use separate lanes for warm-up, repeat-login production, and QA. Teams that skip this step usually overspend or contaminate trust-sensitive work with noisy test traffic.
3. Pick an isolation rule
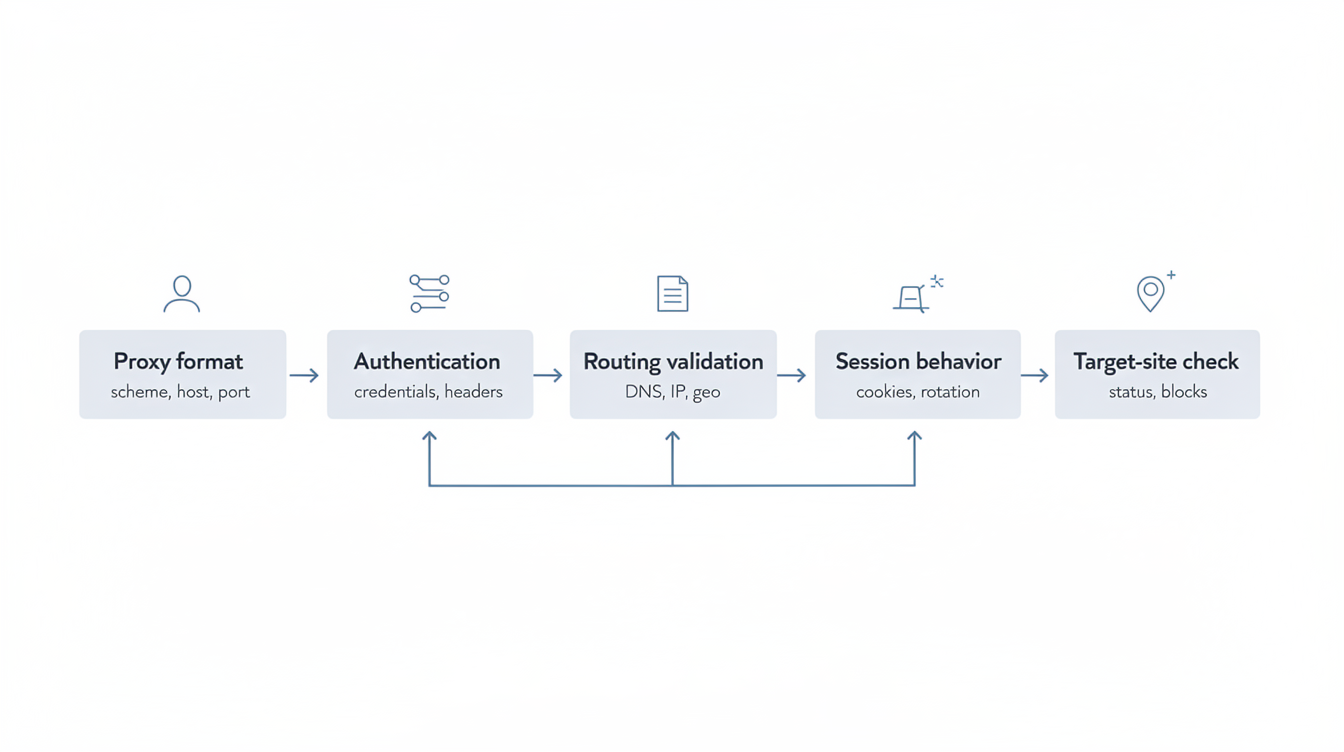
Use one dedicated proxy per identity when failures are expensive. Use shared static proxies only when the target is tolerant and the sessions are short-lived. If you are still validating a provider, run the smaller cohort first using the pass/fail approach in Proxy Trial Checklist.
4. Add a spare pool on purpose
Do not buy exactly the minimum working number. Reserve a few extras for replacement, cooldown, and controlled experiments. A common starting spare is 15 to 30 percent.
5. Review the target’s trust model
If the target behaves more like account defense than raw infrastructure, lean toward more isolation. The broader residential versus datacenter trust tradeoff is covered in Residential vs Datacenter Proxies.
What changes the number up or down
Move the number up when:
- accounts need long-lived continuity over days or weeks
- login or recovery flows are sensitive to IP inconsistency
- operators work overlapping shifts on the same pool
- geography must stay stable per identity
- a failed account costs real time or revenue to repair
Move the number down when:
- the workload is mostly QA, monitoring, or low-friction validation
- active sessions are staggered instead of simultaneous
- you can pause and rotate assignments carefully
- replacement speed matters more than perfect identity continuity
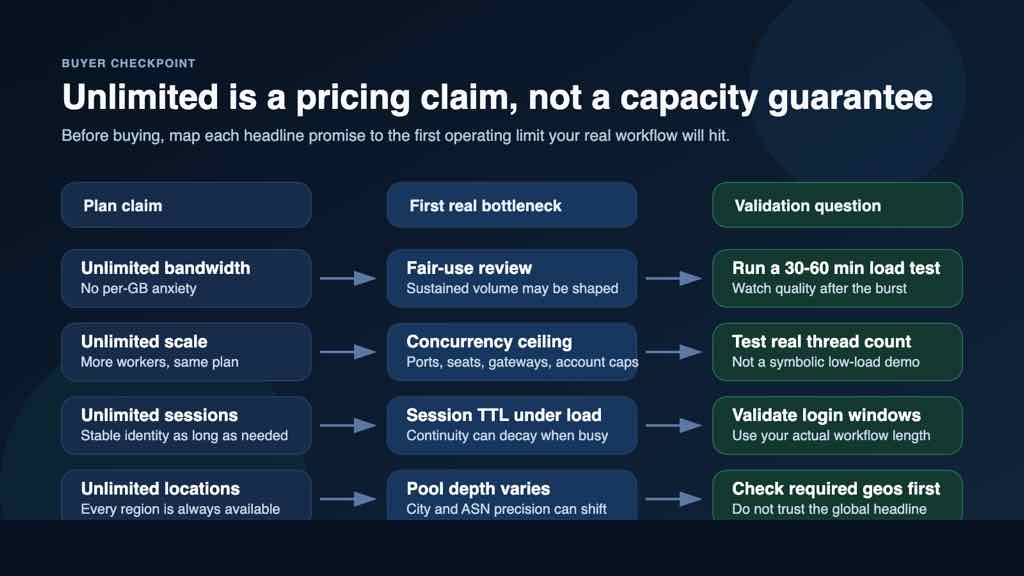
Mistakes that make teams overbuy or underbuy
The most common overbuy mistake is forcing a one-to-one proxy mapping for every total account before concurrency is measured. The most common underbuy mistake is sharing one static proxy across unrelated trust-sensitive identities just because the first login looked fine.
Three other mistakes show up a lot:
- mixing warm-up and QA traffic inside the same batch
- leaving no spare capacity for bad IP replacement or cooldown windows
- deciding from a single clean login instead of a multi-day session pattern
Final planning checklist
Use this before you buy:
- I counted concurrently active identities, not total stored accounts.
- I separated warm-up, repeat-login, and QA work into different sizing lanes.
- I decided whether each lane needs dedicated or shared static proxies.
- I added a spare ratio for replacement and test runs.
- I checked whether the workflow is trust-sensitive enough to justify more isolation.
- I can explain why my first batch size is the minimum safe number, not a guess.
Bottom line
Most teams should start by sizing static proxies around active identity concurrency, then add a deliberate spare pool. Buy more isolation when account continuity is expensive, and buy fewer but better-managed proxies when the work is mostly QA or controlled monitoring.
That gives you a starting batch you can defend operationally instead of a random number that only looked safe in a spreadsheet.