Rotating Residential Proxies Architecture Validation and Cost Per Success Engineering Guide
Rotating Residential Proxies are often evaluated by pool size and price per gigabyte. That mental model fails under real concurrency, real anti-bot detection systems, and real retry pressure.
Engineers working with Rotating Residential Proxies must think in terms of entropy under load, session continuity, ASN diversity, rate limiting thresholds, and cost per successful request. Rotation is not simply IP churn. It is probabilistic identity distribution constrained by infrastructure saturation and reputation decay.
This guide treats residential IP rotation as a distributed systems problem rather than a marketing feature.
Why Rotating Residential Proxies Require an Engineering Mental Model
Residential IP rotation operates across multiple interacting layers:
- Application request patterns
- Session lifecycle behavior
- Exit node allocation
- ASN concentration
- Target rate limiting systems
- Retry amplification
Most surface-level guides reduce the topic to large IP pool size. That is incomplete.
Effective identity entropy depends on:
- Distribution across autonomous systems
- Geo targeting accuracy
- Session reuse ratios
- Proxy session TTL enforcement
- IP reputation half-life
For HTTP semantics and server behavior under load, refer to the IETF HTTP core specification in RFC 9110.
Rotation without shaping produces collapse.
The Architecture of Rotating Residential Proxy Systems
Control Plane Versus Data Plane Behavior
The control plane governs:
- IP allocation strategy
- Residential IP rotation cadence
- Sticky session configuration
- Geo targeting constraints
- Authentication policy
The data plane carries:
- TCP flows
- TLS handshake
- HTTP request headers
- Response codes
When engineers conflate these layers, they misattribute failures.
Teams comparing rotation types across architectures can contrast behaviors described in Residential Proxies, where origin authenticity and ASN spread directly influence detection probability.
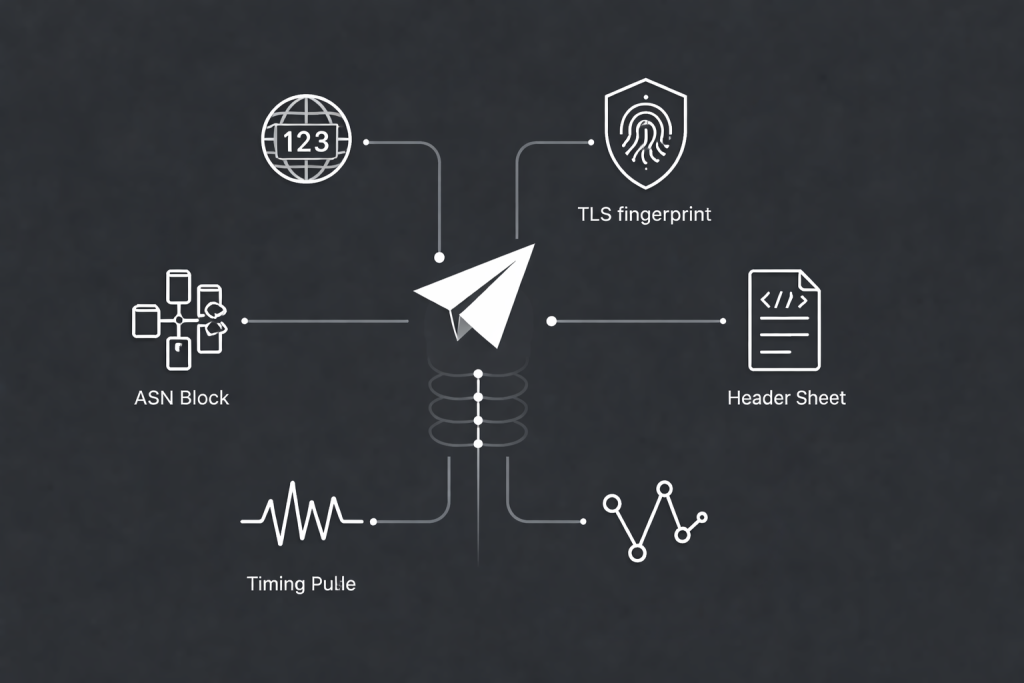
Where Identity Actually Lives
Identity does not live solely in the IP.
It spans:
- IP address
- ASN ownership
- TLS fingerprint
- Header ordering
- Timing signature
- Cookie continuity
For TLS handshake structure and cryptographic negotiation details, see RFC 8446.
Rotating only the IP while keeping timing and TLS fingerprints constant creates detectable asymmetry.
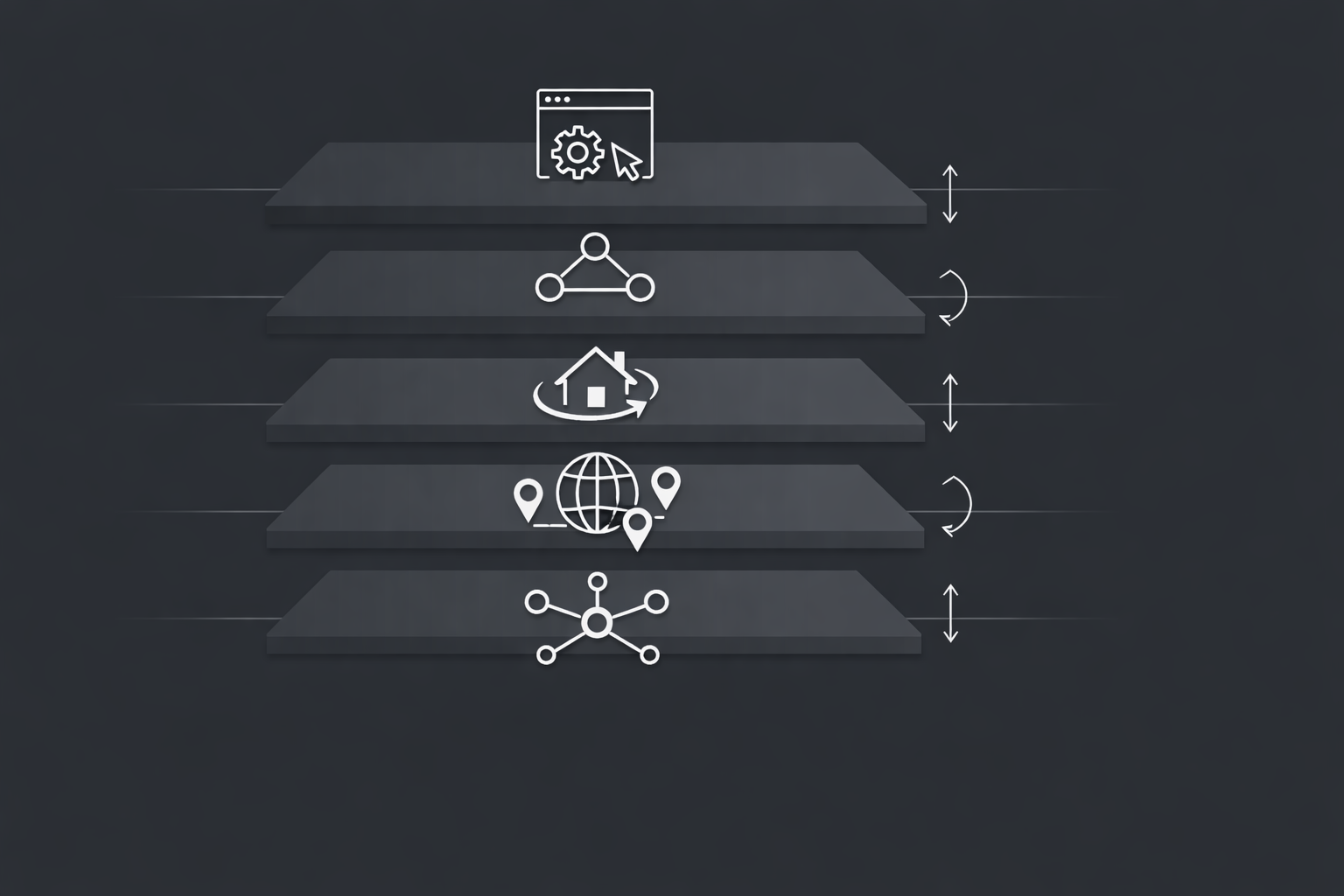
Visual Diagram Suggestion One
16:9 mental model layer stack.
Application behavior
Session orchestration
IP rotation engine
ASN and geo distribution
Transport and TCP layer
Add feedback arrow from 429 signals to concurrency shaping logic.
Failure Modes in Rotating Residential Proxy Deployments
Most failures are systemic, not random.

Failure Mode Matrix
| Symptom | Likely Cause | Signal | First Mitigation |
|---|---|---|---|
| 403 block increase | Reputation clustering | ASN reuse ratio | Lower concurrency per ASN |
| 429 surge | Domain rate limiting | Retry-After header frequency | Adaptive backoff |
| Latency spike | Exit node congestion | p95 histogram growth | Shard across geo |
| CAPTCHA escalation | Session instability | Sticky mismatch | Adjust session TTL |
| Success decay at scale | Pool saturation | Unique IP entropy drop | Reduce parallelism |
Understanding HTTP 429 semantics is critical. Cloudflare documents rate limiting behavior and Retry-After handling in their guide to HTTP 429 Too Many Requests.
Treat 429 as structural feedback, not noise.
Validation Methodology for Rotating Residential Proxies Under Load
Marketing claims are irrelevant without empirical validation.
Baseline Low Concurrency Test
- 1 to 5 requests per second
- Track success rate
- Measure IP entropy distribution
- Record ASN diversity
Concurrency Ramp Test
Increase parallelism gradually:
10 → 25 → 50 → 100 workers
Track:
- Success rate slope
- Retry inflation
- Latency distribution
- Unique IP reuse frequency
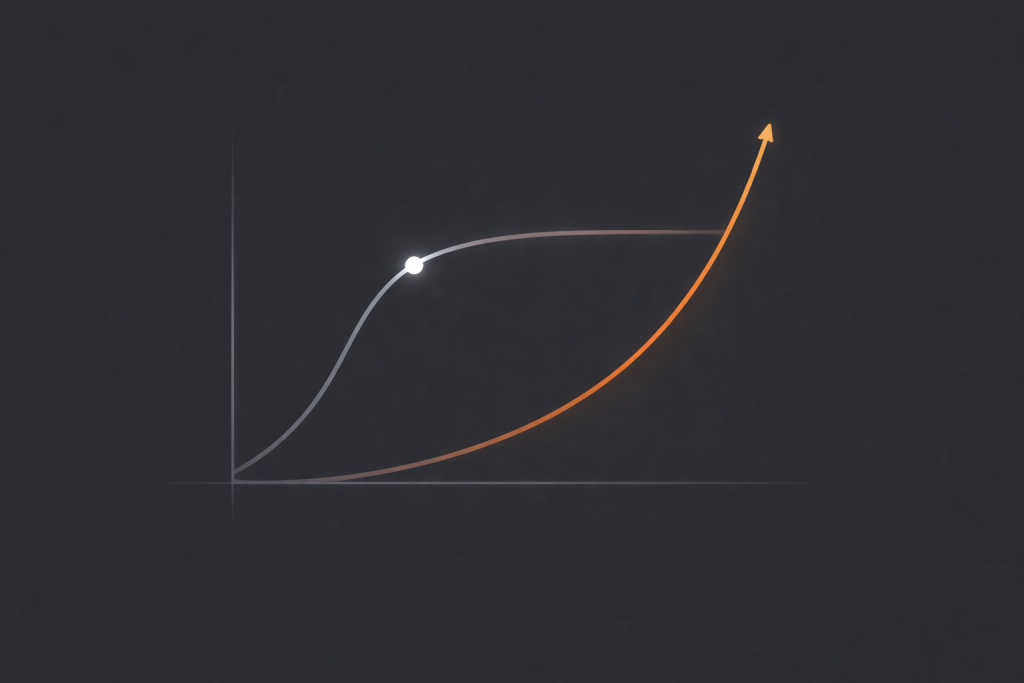
The saturation knee is where retry amplification accelerates faster than success growth.
Soak Testing for Reputation Decay
Run 24 to 72 hours continuously.
Measure:
- ASN drift
- IP reuse compression
- Block rate progression
- Geo targeting consistency
Residential IP rotation stability depends less on headline pool size and more on ASN spread and subnet churn control.
Geo and ASN Stability Audit
Geo targeting claims must match observed geolocation.
Verify using external geo databases and ASN lookup tools.
Visual Diagram Suggestion Two
16:9 concurrency versus success curve.
X-axis concurrency.
Y-axis success rate.
Overlay retry inflation curve.
Mark saturation knee.
Concurrency Shaping Strategies for Residential IP Rotation
Linear scaling fails because infrastructure ceilings are non-linear.
Why Parallel Requests Trigger Collapse
Common causes:
- Shared ISP subnet capacity
- ASN-level detection thresholds
- Exit node queueing
- Session TTL churn
Concurrency must be shaped at:
- Per IP level
- Per ASN level
- Per domain level
Adaptive token bucket and feedback-based concurrency controllers outperform static worker pools.
Rotation cadence considerations align with behaviors described in Rotating Proxies, particularly when comparing per-request rotation versus sticky allocation.
Sticky Sessions Versus Per Request Rotation
Sticky sessions improve continuity for:
- Account workflows
- Multi-step checkout scraping
- Login state persistence
But they increase fingerprint consistency risk.
Proxy session TTL tuning is critical for long workflows with geo targeting constraints.
429 Handling and Retry Backoff Engineering
Ignoring rate limiting destroys cost efficiency.
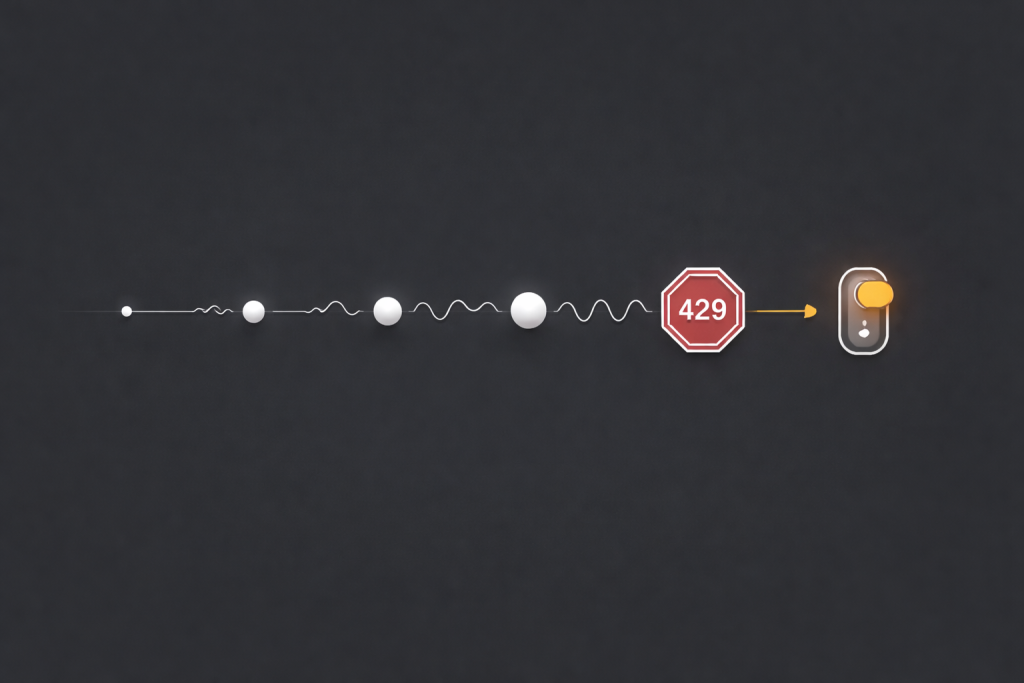
Adaptive Retry Backoff
Best practice includes:
- Exponential backoff
- Random jitter
- Domain-specific queues
- Circuit breaker thresholds
Retry logic should parse Retry-After headers when present.
The semantics of retry guidance are formally defined in RFC 6585.
Retry Inflation as Hidden Economic Leakage
If success rate drops from 95 percent to 80 percent, retries increase bandwidth consumption disproportionately.
This increases:
- IP churn
- Infrastructure load
- Cost per success
Residential IP rotation must be evaluated under retry amplification, not raw success rate.
Visual Diagram Suggestion Three
16:9 retry timeline diagram.
Requests spaced progressively wider.
Add jitter variation marks.
Include circuit breaker threshold icon.
Cost Per Success Economic Modeling for Residential IP Rotation
Per-gigabyte pricing obscures operational economics.

Cost Per Success Formula
Cost per success equals total proxy spend plus retry overhead plus compute divided by successful responses.
Variables include:
- Success rate under concurrency
- Retry amplification factor
- Average response payload size
- CAPTCHA solve cost
- Session reset overhead
Delivered Capacity Versus Advertised Pool Size
Advertised IP pool size may appear massive.
Effective concurrent usable entropy is the real metric.
Engineers should calculate unique IPs observed per minute under peak load rather than relying on marketing figures.
Geo Targeting and ASN Stability Under Detection Systems
Geo Targeting Accuracy Verification
Validate:
- Country resolution
- City accuracy
- ISP consistency
Geo mismatches increase anti-bot detection risk in regional pricing intelligence and localized scraping workflows.
ASN Stability and Detection Risk
Anti-bot systems evaluate:
- ASN clustering
- Traffic burst signatures
- Historical abuse metrics
Residential IP rotation concentrated in a narrow ASN band increases detection probability.
Proxy Authentication and Session Hygiene
Authentication methods impact system stability.
Credential exhaustion can manifest as:
- 407 proxy authentication responses
- Unexpected disconnects
- Session resets
Session hygiene strategies include:
- Controlled TTL refresh
- Per-domain credential isolation
- Monitoring authentication failure rate
Decision Framework for Technical Buyers
Evaluate rotating residential proxies using measurable criteria:
- Entropy retention under concurrency ramp
- ASN diversity distribution
- Retry inflation slope
- Geo targeting stability
- Cost per success consistency
- Sticky session reliability
- Authentication resilience
Avoid success metrics presented without concurrency context.
Engineering Playbook for Stable Rotation at Scale
- Start at low concurrency
- Measure entropy and ASN distribution
- Ramp gradually
- Monitor retry slope
- Respect 429 feedback
- Optimize cost per success, not bandwidth cost
Workloads that demand sustained identity continuity under pressure require structured concurrency control and measured residential IP rotation rather than blind parallel scaling.
Daniel Harris is a Content Manager and Full-Stack SEO Specialist with 7+ years of hands-on experience across content strategy and technical SEO. He writes about proxy usage in everyday workflows, including SEO checks, ad previews, pricing scans, and multi-account work. He’s drawn to systems that stay consistent over time and writing that stays calm, concrete, and readable. Outside work, Daniel is usually exploring new tools, outlining future pieces, or getting lost in a long book.
FAQ
1.How large should an IP pool be for stable rotation?
Large enough to maintain entropy under peak concurrency, not just headline size.
2.How long should proxy session TTL be?
Long enough for workflow continuity but short enough to prevent fingerprint drift.
3.When should sticky sessions be used?
For stateful multi-step interactions where identity continuity outweighs entropy.
4.What retry rate is acceptable?
Below the point where retry amplification materially increases cost per success.
5.How important is ASN diversity?
Critical for reducing clustering risk and detection probability.






