Shared vs Dedicated Proxies: Which One Fits Team QA, Account Isolation, and Budget Control?
Shared proxies are usually the cheaper starting point, but dedicated proxies are often the safer decision when one workflow needs stable ownership and repeatable results. If a bad session only costs you one retry, shared can be fine. If it costs analyst time, account trust, or a broken QA run, dedicated is usually worth the premium.
Decision table: when shared or dedicated is the better fit
| Buying question | Shared proxies are usually enough when… | Dedicated proxies are usually better when… |
|---|---|---|
| Who uses the IPs? | A broad pool can be reused across disposable tasks | One team, account set, or workflow needs clear ownership |
| How costly is interference? | Retries are acceptable and false signals are cheap | Mixed traffic would make debugging, rate limits, or trust issues expensive |
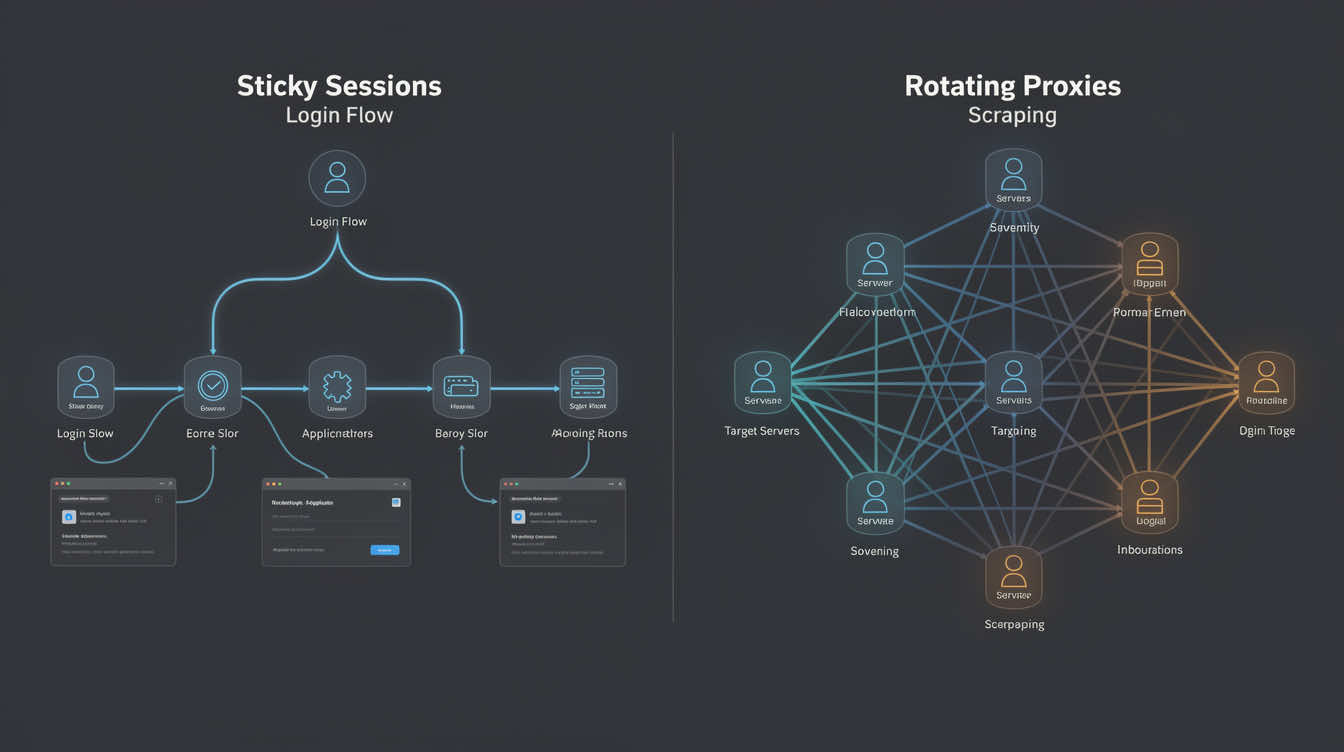
| Do sessions need continuity? | Sessions are short and identity continuity does not matter much | Long-lived logins, warm-up, or recurring account actions need consistency |
| How sensitive is the workflow? | Tasks are low-risk, exploratory, or one-off | QA, seller checks, account ops, or buyer journeys need reproducibility |
| What matters more this month? | Lower entry cost and flexible broad coverage | Cleaner accountability and lower hidden ops cost |
In practice, this is less about the label and more about who owns the failure when a result looks wrong. If multiple users share the same pool, it becomes harder to tell whether the issue came from the target site, your tooling, or traffic from someone else. That is why this decision sits closer to workflow design than simple pricing.
If you are still sizing session inventory, the planning logic in How Many Static Proxies Do You Need? pairs well with this ownership decision.
What shared proxies usually save, and where they create hidden cost
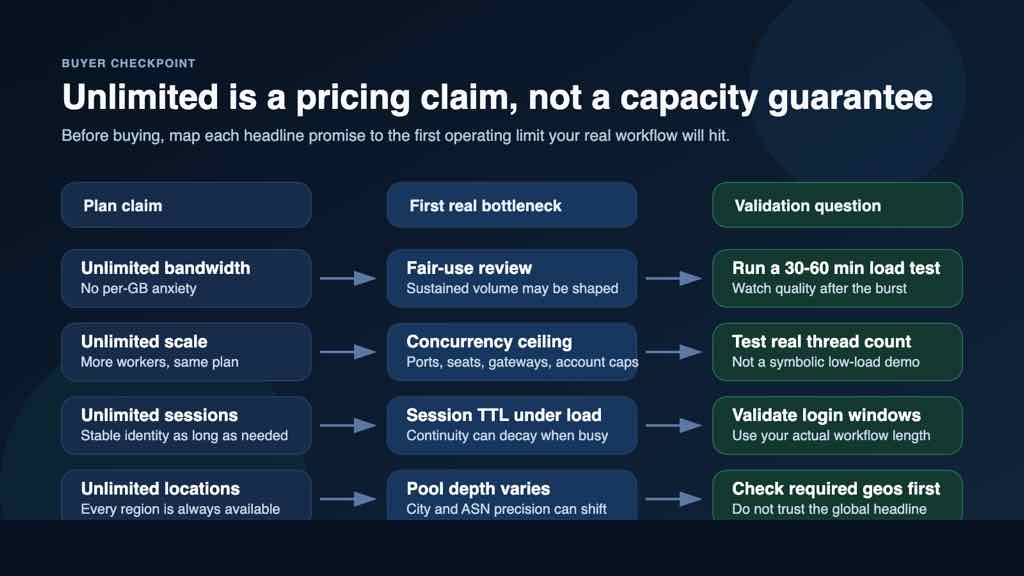
Shared proxies lower the upfront commitment. They are useful when you need broad access for testing ideas, validating geo reach, or running low-stakes tasks where occasional retries are normal. For many lightweight jobs, that is a perfectly rational trade.
The problem is that cheap headline access can hide expensive ambiguity. If several users touch the same pool, you may see uneven performance, session contamination, or trust-score swings that are difficult to attribute. The loss is not always bandwidth or speed. It is often operator time spent asking whether the proxy itself changed the outcome.
That is why a shared plan can look cheaper on paper and still cost more in real use. The same mindset shows up in Proxy Ports vs IP Count: the headline resource number rarely tells the full operational story.
When dedicated proxies pay for themselves
Dedicated proxies become attractive when ownership clarity matters more than the smallest monthly invoice. If one team controls the IPs, you get cleaner debugging, more predictable warm-up behavior, and better accountability when a login, checkout, or monitor starts failing.
They are especially useful for workflows that depend on continuity: repeat logins, seller or merchant QA, long-lived browser profiles, and any account-sensitive operation where you want fewer unknowns. In those cases, exclusive allocation is not a luxury. It is part of risk control.
If this sounds like a stable-session workflow, Static Proxies and Static Residential Proxies are the natural product families to compare first.
A 4-step way to choose before you buy
- Define the unit that needs ownership. Decide whether the resource belongs to a person, an account cluster, a browser profile set, or a monitoring lane. If you cannot name the owner, shared is often still acceptable.
- Price the cost of interference. Ask what one bad or ambiguous session actually costs. If it burns minutes, analyst trust, or account reputation, move the candidate toward dedicated.
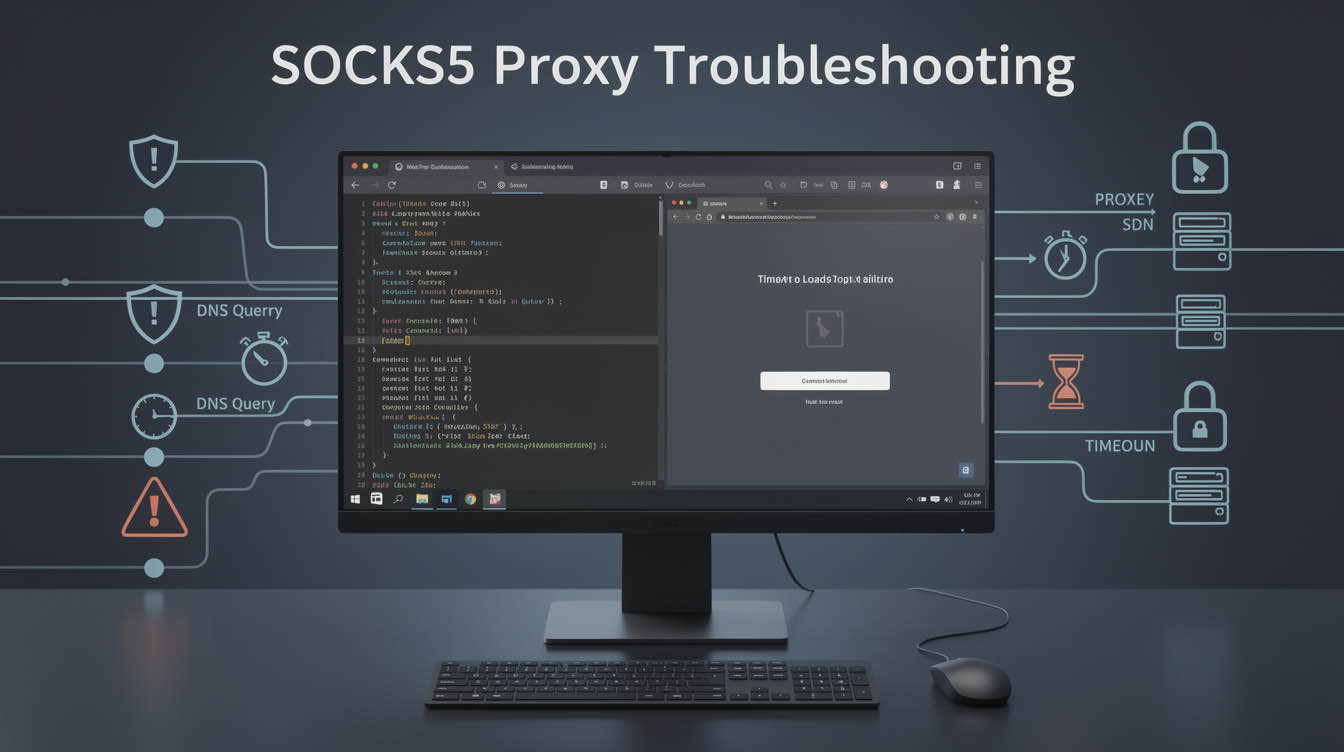
- Check continuity requirements. If the same identity needs to come back predictably, shared pools become less attractive. For auth-sensitive work, use the checks in Proxy Authentication Checklist before rollout.
- Compare real monthly cost, not just list price. Add retries, failed runs, investigation time, and spare capacity. A dedicated plan that prevents repeated rework can be the cheaper system overall.
Pre-launch checklist before you lock in the plan
- Confirm whether the allocation is truly exclusive or only less crowded than standard shared stock.
- Verify how replacements work if an IP is burned or underperforming.
- Match the auth model to the team workflow so ownership and access are easy to audit.
- Decide whether each workflow needs a fixed assignment or a wider pool with rules.
- Keep a spare ratio so one bad IP does not stall the whole lane.
- Test the exact target actions that matter, not just a homepage request.
Where MaskProxy product types fit naturally
Use Residential Proxies when trust realism matters more than raw throughput, especially for buyer journeys or account-sensitive checks. Use Static Datacenter Proxies when you want predictable ownership and cleaner cost for stable, lower-risk automation or QA lanes.
If you do not need persistent identity and you mainly care about broad distribution, Rotating Proxies may be a better comparison set than dedicated static inventory.
Conclusion
Choose shared proxies when the work is disposable, retry-friendly, and cheap to misread. Choose dedicated proxies when continuity, accountability, and session ownership directly affect business results. The best buying question is not “Which one is cheaper?” It is “Which failure mode can my workflow afford?”