HTTP 429 After Proxy Rotation: IP Pool or Request Pacing?
HTTP 429 after proxy rotation usually means the target still sees too much activity inside its rate-limit window. The proxy may be part of the problem, but changing IPs is the wrong first move until you know whether the limit follows request pace, account identity, cookies, headers, session design, or a small group of weak exit IPs.
The fastest useful diagnosis is simple: keep the same target, same endpoint, and same task, then change one variable at a time. If lowering the request rate fixes 429 across both one IP and many IPs, the bottleneck is pacing. If only specific exits fail under the same pace, the pool or targeting setup deserves closer inspection.
Start with the answer: 429 usually means the target still sees too much activity
MDN describes HTTP 429 as “Too Many Requests”: the client has sent too many requests in a given time, and the response may include a Retry-After header. That definition matters because it puts rate policy before proxy quality in the diagnosis.
A rotating proxy changes the network exit. It does not automatically reset every signal the target may use to count activity. The target can still group requests by:
- account or API token;
- session cookie or browser storage;
- TLS/browser fingerprint;
- User-Agent and header pattern;
- endpoint, query pattern, or payload shape;
- ASN, country, city, or proxy reputation segment;
- concurrency and retry behavior.
For teams running scraping, monitoring, or browser automation, the practical question is not “does rotation work?” The question is “which signal is the target counting when it returns 429?” If you answer that first, the fix becomes smaller and safer.
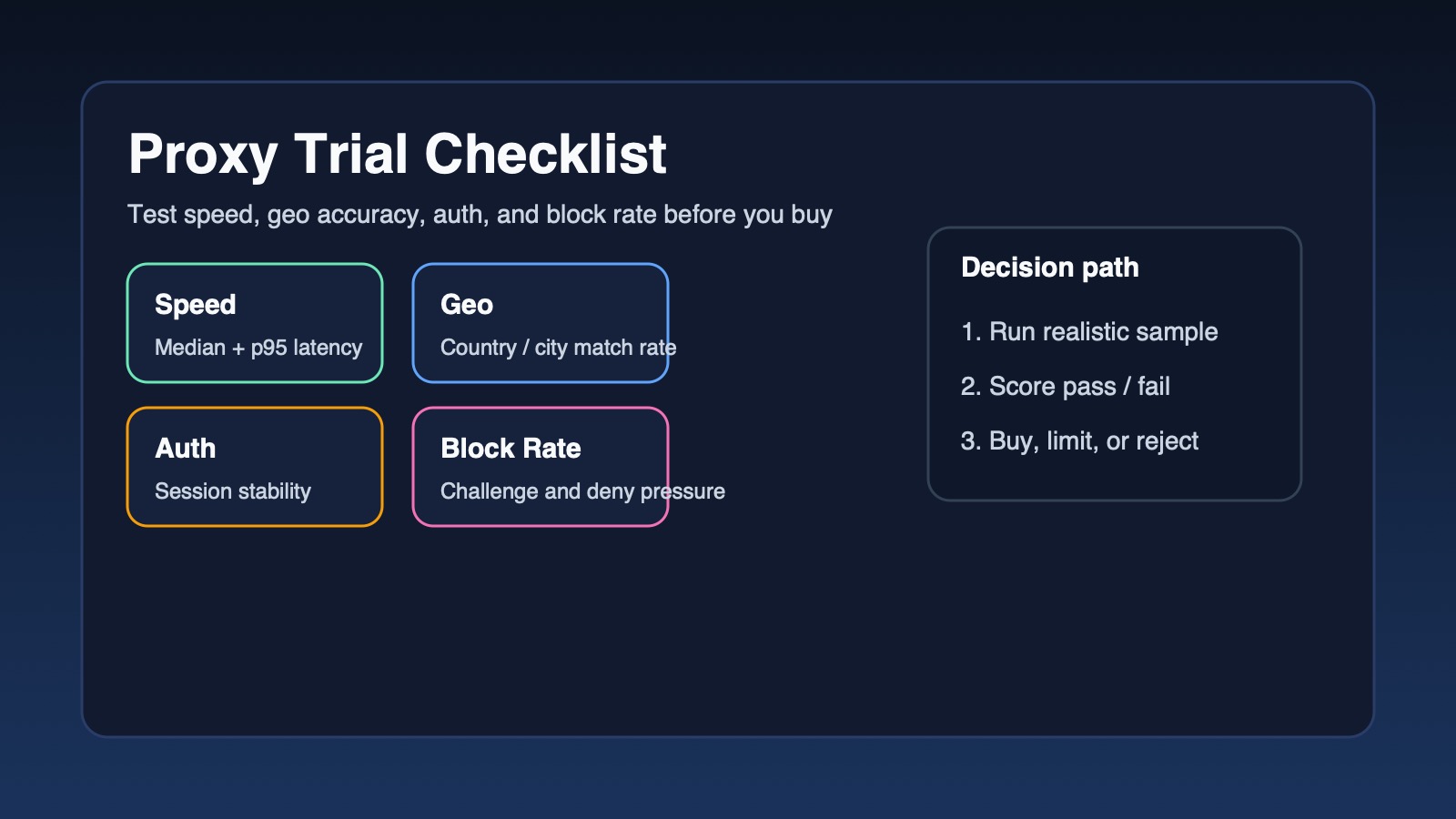
Run a four-cell test before changing providers
Use a small test matrix before buying more IPs or rewriting the whole crawler. Keep logging exact timestamps, status codes, exit IP, account/session ID, endpoint, and response headers. Run each cell long enough to cross the target’s normal rate window.
| Test cell | What you change | What a 429 result suggests | Next action |
|---|---|---|---|
| One IP, current pace | Nothing except controlled logging | Baseline failure rate | Capture Retry-After, endpoint, and concurrency |
| One IP, lower pace | Reduce requests and concurrency | If 429 drops, pacing is dominant | Respect the slower window before scaling |
| Many IPs, current pace | Rotate exits but keep pace | If 429 remains, target may count account/session or request pattern | Inspect cookies, tokens, headers, and retry bursts |
| Many IPs, lower pace | Rotate exits and reduce pace | If only some exits fail, pool fit or reputation may matter | Compare exit ASN, geo, and success rate by IP group |
This matrix prevents two common mistakes. First, it stops teams from treating every 429 as proof that the proxy pool is bad. Second, it stops teams from slowing the crawler unnecessarily when the real problem is a narrow set of exits or an accidental sticky-session setting.
Check whether cookies, accounts, or headers carry the same identity
If every rotated IP receives 429 after the same login, token, or browser profile is reused, the limit may be tied to identity rather than IP. In that case, rotating faster can make the pattern look more suspicious because the same account appears from many locations in a short period.
Check these signals before changing proxy settings:
- Run the same request with a clean cookie jar and a separate test account where policy allows it.
- Compare authenticated and unauthenticated endpoints.
- Log whether 429 appears after a fixed number of account actions rather than a fixed number of IP requests.
- Stop automatic retries that fire immediately after a 429; they often consume the next window and make the limit persist.
- Preserve normal browser headers instead of sending a different header set on each retry.
A proxy can route traffic, but it cannot make one account look like many independent users if the workflow keeps the same account, cart, token, or device state. When 429 follows the account, the fix is usually lower pacing, cleaner queueing, and a better retry schedule, not more aggressive IP rotation.
Separate sticky-session design from real rotation
Many proxy setups support both sticky sessions and rotating sessions. Sticky sessions are useful for login continuity, carts, checkout testing, and workflows that break when the IP changes mid-session. They are a poor fit for high-frequency endpoint polling when the target applies a short per-IP window.
Verify the session behavior directly:
- Print the observed exit IP for every request, not only the configured proxy endpoint.
- Confirm whether the provider rotates per request, per time window, per session ID, or only when the connection is reopened.
- Check whether connection pooling in your HTTP client is reusing the same proxy tunnel longer than expected.
- Test with a new proxy session identifier and a closed connection pool.
- Compare browser automation traffic with simple command-line requests to rule out framework-level connection reuse.
If the same exit IP appears across the whole burst, the 429 may be expected. If exits change but the same session cookie stays attached, IP rotation is working but the target still has a stable identity signal.
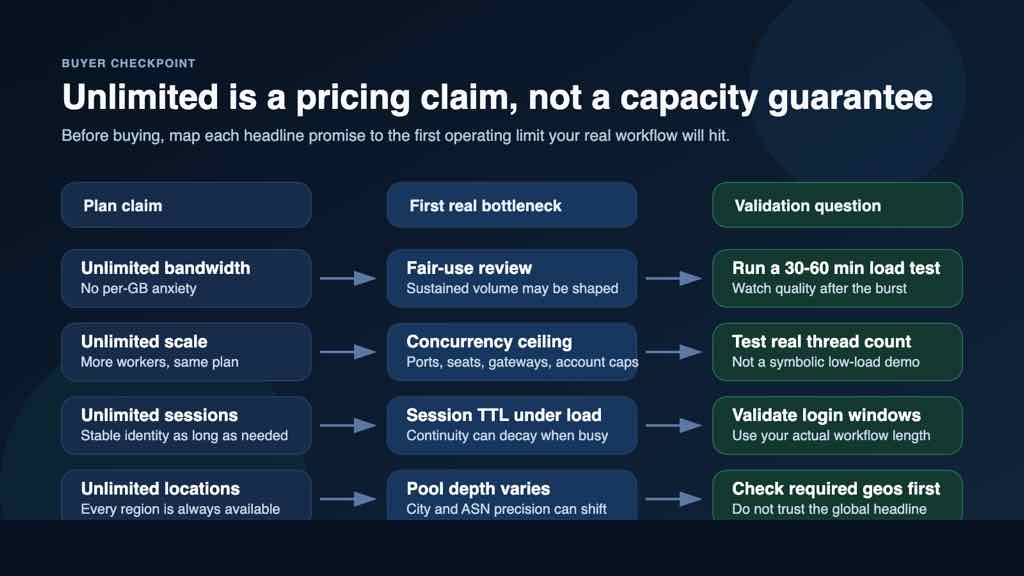
For workflows where the diagnosis points to pool diversity rather than code behavior, compare location and rotation controls against rotating residential proxy options for variable exit IP workflows. Use that comparison only after the test matrix shows a pool-side bottleneck.
Decide when the proxy pool is the problem
The proxy pool becomes the main suspect when the failure pattern is tied to exit properties under controlled pacing. Look for evidence such as:
- the same target accepts your reduced request rate from some exits but not others;
- 429 appears immediately on first request for a subset of IPs;
- failures cluster by ASN, country, city, or datacenter/residential segment;
- a fresh account, clean cookies, and conservative pace still fail only on specific exits;
- retries through the same exit fail, while retries through a different exit at the same pace succeed.
At that point, the useful action is targeted validation. Do not only count how many IPs are available. Track success rate by exit group, time of day, location, and endpoint. A smaller pool that matches the target’s geography and session needs can outperform a larger pool that produces inconsistent status codes.
If you need to compare available proxy types, use the site’s proxy product navigation by rotation and session needs as a starting point, then validate the specific product fit with your own target, headers, accounts, and pacing rules.
Build a safe rollout plan after the fix
Once the failing branch is clear, apply the smallest fix and retest. A safe sequence looks like this:
- Respect
Retry-Afterwhen it is present. - Add jitter instead of sending evenly spaced machine-like bursts.
- Cap concurrency per account, per endpoint, and per exit IP.
- Keep sticky sessions only where continuity is required.
- Rotate exits deliberately for stateless collection, not inside a logged-in action that expects continuity.
- Store 429 rate, success rate, response time, and exit metadata in the same log row.
- Scale volume in steps after the 429 rate stays stable under the new settings.
The decision point is straightforward: if pacing changes fix the issue, keep the current proxy setup and slow the workload. If identity carryover fixes the issue, isolate accounts and sessions more carefully. If controlled tests show exit-specific failures, change the pool, location, or rotation mode with evidence instead of guessing.